- English
- 日本語
Encrypting logs
Last updated 2019-10-23
For supported logging endpoints, Fastly allows you to encrypt your log files before they are written to disk. The files are encrypted using OpenPGP (Pretty Good Privacy).
IMPORTANT
Be sure to take into account security, privacy, and compliance requirements when making configuration and endpoint decisions for the data you intend to include in streamed logs.
Generating a PGP key pair
To use this feature, you'll need to use a PGP implementation (such as GPG) to generate a public and private PGP key pair. Typically, this involves running the following command in a terminal application on your personal computer:
$ gpg --gen-keyFollow the instructions shown in your terminal application. Enter your email address and set a passphrase when prompted. Remember the values you enter.
WARNING
Keep your private key safe! If you lose it, your encrypted log files will be permanently unreadable.
Exporting the PGP public key
After you generate the PGP key pair, you'll need to export your public key. Typically, this involves running the following command in a terminal application on your personal computer:
$ gpg --armor --export <your email>The output will be in PEM (Privacy-Enhanced Mail) format and will look similar to the following:
-----BEGIN PGP PUBLIC KEY BLOCK-----mQGiBFciSsYRBAC9aHsraEzLmzfuQLx+BZmGTCOQFsPGpiPaEKrulRbrcBvtt3BlzajFP9iVzSm3+Zyqge/1AtHllSnPHTqG2EoBCsWtXL/JnZcPjx8c5r8G5IuBGrh8snP3KTJ64zCS7PUvrWy5RWcJ6Rs+6wiJ7zPOtU5wMEPuMbflh/soy50zrwCg74XN[...REDACTED...]-----END PGP PUBLIC KEY BLOCK-----Enabling log encryption
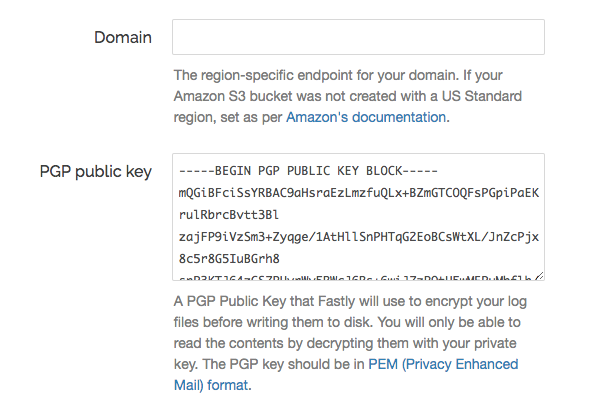
To enable PGP encryption for a logging endpoint that supports it, copy and paste your public PGP key into the PGP public key field in the Fastly control panel when creating or editing a supported logging endpoint.
Decrypting log files
To read an encrypted log file, you'll need to download and decrypt it. Typically, this involves running the following command in a terminal application on your personal computer:
$ gpg --decrypt <encrypted log file>Enter your passphrase to decrypt the log file.
Do not use this form to send sensitive information. If you need assistance, contact support. This form is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.