Redacting data
Last updated 2024-08-28
To maintain data privacy, Next-Gen WAF redacts sensitive data from requests before they reach the platform backend.
Selective data transfer and redaction
The Next-Gen WAF agent filters requests locally to determine if they contain an attack. Only requests that are marked as attacks or anomalies are then sent to the platform backend after additional filtering and sanitizing are done. Once the agent identifies a potential attack or anomaly in a request, the agent sends only the individual parameter of the request which contains the attack payload, as well as a few other non-sensitive or benign portions of the request (e.g., client IP, user agent, or URI). The entire request is never sent to the platform backend. Additionally, specific portions of the request are automatically redacted and never sent to the backend, including tokens, credentials, and known patterns such as credit card and social security numbers.
JSON API payloads
Next-Gen WAF automatically parses JSON key-value pairs and treats them like request parameters. The following sample requests demonstrate how redactions work within the context of a request.
The initial request:
POST /request HTTP/1.1Content-Length: 72Content-Type: application/jsonHost: api.example.com{"user":"user@api.example.com","password":"<script>alert(1)</script>mypassword","zip":94089}What's sent to the Next-Gen WAF:
POST /request HTTP/1.1Host: api.example.com
password=The initial request:
POST /request HTTP/1.1Content-Length: 72Content-Type: application/jsonHost: api.example.com
{"user":"user@api.example.com","password":"mypassword","zip":"<script>alert(1)</script>94089"}What's sent to the Next-Gen WAF:
POST /request HTTP/1.1Host: api.example.com
zip=<script>alert(1)</script>Sensitive headers
Next-Gen WAF redacts the following from requests:
- Explicit names:
authorization,x-auth-token,cookie,set-cookie - Any names that contain:
-token,-auth,-key,-sess,-pass,-secret - Query strings from
refererandlocation
The initial request:
POST /example?sort=ascending HTTP/1.1Host: example.comUser-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.10; rv:35.0)Accept: text/html, application/xhtml+xmlContent-Length: 57Cookie: foo=bar
sensitive=hunter2&foobar=<script>alert(1)</script>&page=3What’s sent to the Next-Gen WAF:
POST /example HTTP/1.1Host: example.comUser-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.10; rv:35.0)
foobar=<script>alert(1)</script>Sensitive parameters
If a request contains an attack or anomaly, and also contains sensitive data in commonly-used parameter names, Next-Gen WAF will redact the entire contents of the sensitive parameter. These parameters include:
api_keypasswordpasswdpasspwuserloginloginidusernameemailkeyidsidtokenrequest_tokenaccess_tokencsrfmiddlewaretokenoauth_verifierconfirm_passwordpassword_confirmation
The initial request:
POST /example HTTP/1.1
username=<script>alert("jsmith")</script>What’s sent to the Next-Gen WAF:
POST /example HTTP/1.1
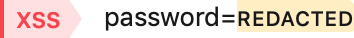
username=[redacted]The control panel clearly displays which parameters have been redacted. Redacted parameters are replaced with the word REDACTED highlighted in yellow.
Sensitive patterns
Next-Gen WAF automatically redacts known patterns of sensitive information, which includes the following:
- Credit card numbers: values like
4111-1111-1111-1111become0000-0000-0000-0000 - Social security numbers: values like
078-05-1120become000-00-0000 - GUIDs: values like
3F2504E0-4F89-41D3-9A0C-0305E82C3301become0000000-0000-0000-0000-000000000000 - Bank account (IBAN) numbers: values like
DE75512108001245126199becomeAA00aaaa0000000
The initial request:
POST /example HTTP/1.1
credit_card_example=<script>alert("4111-1111-1111-1111")</script>What’s sent to the Next-Gen WAF:
POST /example HTTP/1.1
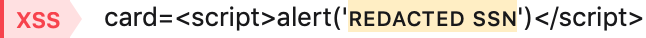
credit_card_example=<script>alert("0000-0000-0000-0000")</script>Within the control panel we clearly display which patterns have been redacted. Redacted patterns are replaced with the word REDACTED highlighted in yellow.
Custom redactions
In addition to the redactions listed above, you can also specify additional fields to redact from requests. For example, if your password field is named foobar instead of password, that field can be specified for redaction.
IMPORTANT
Accounts are limited to 100 redactions per site (also known as workspace).
Creating custom redactions
When you have a sensitive field that is not filtered out by default, you can create a custom field redaction:
- Next-Gen WAF control panel
- Fastly control panel
- Log in to the Next-Gen WAF control panel.
- From the Sites menu, select a site if you have more than one site.
- From the Rules menu, select Redactions.
- Click Add redaction.
- In the Field name field, enter the name of the field to be redacted.
- From the Field type menu, select the type of field to be redacted. Options include Request parameter, Request header, or Response header.
- Click Create redaction.
Editing custom redactions
To edit a custom redaction, complete the following steps:
- Next-Gen WAF control panel
- Fastly control panel
- Log in to the Next-Gen WAF control panel.
- From the Sites menu, select a site if you have more than one site.
- From the Rules menu, select Redactions.
- Click View to the right of the custom redaction you want to edit.
- Click Edit redaction.
- Change the Field name and Field type as needed.
- Click Update redaction.
Deleting custom redactions
- Next-Gen WAF control panel
- Fastly control panel
- Log in to the Next-Gen WAF control panel.
- From the Sites menu, select a site if you have more than one site.
- From the Site Rules menu, select Redactions.
- Click View to the right of the custom redaction you want to delete.
- Click Remove redaction.
- Click Delete to delete the redaction.
Transparency
To allow for easy verification of what the agent sends to the backend, we provide a way to view all agent to backend communication.
Verifying in the control panel
To verify our agents are correctly filtering and sanitizing requests, we provide a raw log of data that’s sent from our agents:
- Next-Gen WAF control panel
- Fastly control panel
- Log in to the Next-Gen WAF control panel.
- From the Sites menu, select a site if you have more than one site.
- Click on Agents.
- Click on the Agent ID.
- Click the Requests tab.
- Review the requests and verify that data is correctly redacted.
Verifying with the agent
IMPORTANT
Only customers with access to the Next-Gen WAF control panel can use the debug-log-uploads setting to verify redactions. If you have access to the Next-Gen WAF product in the Fastly control panel, use the Fastly control panel to verify redactions.
You can also verify directly from the agent itself by setting the debug-log-uploads agent configuration option. For example, if you want to log all agent uploads in formatted JSON, add the following line to your agent configuration file (by default at /etc/sigsci/agent.conf):
debug-log-uploads = 2Do not use this form to send sensitive information. If you need assistance, contact support. This form is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.