Setting up single sign-on (SSO)
Last updated 2025-04-29
IMPORTANT
This guide only applies to Next-Gen WAF customers with access to the Next-Gen WAF control panel. If you have access to the Next-Gen WAF product in the Fastly control panel, check out our enablement guide for Fastly accounts.
If your company uses an identity provider (IdP) to manage user authentication, you can enable the single sign-on (SSO) feature to either allow or require your organization's users to sign in to the Next-Gen WAF control panel using the IdP instead of an email address and password.
Enabling single sign-on
- SAML 2.0
- OAuth 2.0 services
Start by switching to SAML in the control panel:
- Log in to the Next-Gen WAF control panel.
- From the Corp Manage menu, select User Authentication.
- In the Authentication section, click Switch to SAML to use SAML authentication for providers like Okta or OneLogin.
Then, configure your IdP to use the following settings:
- Recipient/Consumer URL:
https://dashboard.signalsciences.net/saml - Audience URI (SP Entity ID):
https://dashboard.signalsciences.net/ - Consumer URL Validator:
^https:\/\/dashboard\.signalsciences\.net\/saml$
A few things to note if you're self-configuring using SAML 2.0:
- We don't publish SAML metadata.
- You must specify the SAML 2.0 Endpoint and x.509 public certificate from the app configured in your IdP.
- We require a signed SAML Response. SAML Responses that only sign the Assertion will be rejected, so ensure the SAML Response is signed in your IdP configuration.
- You must allow SP-initiated logins to complete the handshake that sets up SAML. Once that's complete, you will be able to use IdP-initiated logins.
- When updating or adding your SAML SSO configuration, the
RelayStatesent in the POST body of the AuthNRequest must be provided back in the SAML Response from your IdP. This completes the handshake that sets up SAML. - If PingFederate is your IdP, you need to deselect the Require authn requests to be signed when received via the post or redirect bindings and Always sign the SAML assertion options under the Signature Policy settings.
After enabling single sign-on
Once you enable SSO, the passwords and 2FA tokens for any existing users will be deleted and all users with active sessions in progress will have those sessions expired.
Each user will be sent an email with an SSO binding link and instructions to set up SSO on their accounts. Any users attempting to log in without clicking the SSO binding link will receive an error message telling them that SSO has been enabled for their corp (account) and to follow the link in their email.
Once users have successfully configured SSO, they will receive an email confirming the change.
Considerations
Keep in mind the following things:
Use a secure cryptographic algorithm. The SHA-1 cryptographic algorithm has been retired by the National Institute of Standards and Technology (NIST) and they recommend upgrading to more advanced and secure replacements such as those from the SHA-2 family of hash functions, like SHA-256. Consider using or upgrading to these more advanced algorithms for SAML certificate signing for SSO setup in advance of the NIST recommended phase out deadline.
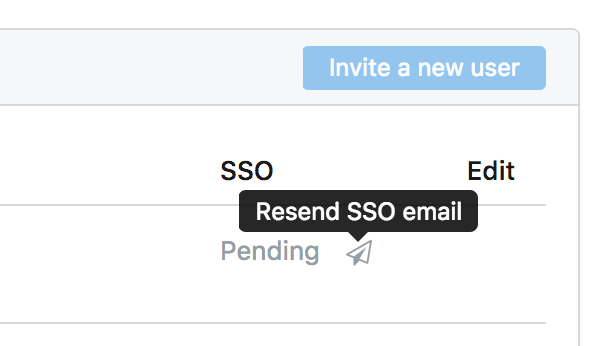
SSO binding links only remain valid for 3 days. If the SSO binding link expires, you can resend it by clicking Resend SSO email next to the Pending SSO status in the Users panel on the User Management page.
The email from your identity provider must match the email in your Signal Sciences account. If the email from your identity provider doesn't match the email in your Signal Sciences account, you will be alerted that your Signal Sciences email will be changed to your identity provider's email when you enable SSO.
If the email you choose doesn't match the email in your Signal Sciences account and conflicts with an email already in the system, you will be shown an error message and be required to choose another email.
When specified, single sign-off follows your IT department's settings. If your corp's (account's) IT department determines you need to use a custom logout URL to handle logout redirects and cookie updates, it is possible to supply an optional logout endpoint. There are no parameters necessary; the browser will do a GET request and follow any sign-out settings or redirects supplied by your IT department.
Disabling single sign-on
Owners can disable single sign-on for all users on the corp (account) by following these steps:
- Log in to the Next-Gen WAF control panel.
- From the Corp Manage menu, select User Authentication.
- To the right of Signal Sciences built-in authentication, click Switch to built-in auth.
- In the Password field, enter your new password. You are required to set a new password for your user before disabling single sign-on to prevent you from being locked out of the Next-Gen WAF control panel.
- Click Continue.
After disabling single sign-on, all other users in your corp (account) will have their active sessions expired. They will receive an email with a link to set a new password, informing them SSO has been disabled. All users will need to set new passwords to log back into the Next-Gen WAF control panel.
Bypassing single sign-on for selected users
If your corp (account) has single sign-on enabled, an Owner user can set a user to bypass SSO for their Signal Sciences account. This allows them to log in to the Next-Gen WAF control panel via their username and password without needing to authenticate through your SSO provider.
- Log in to the Next-Gen WAF control panel.
- From the Corp Manage menu, select Corp Users.
- Click on the user you want to bypass SSO.
- Click Edit corp user.
- Under Authentication, select Allow this user to bypass Single Sign-On (SSO).
- Click Update user.
Do not use this form to send sensitive information. If you need assistance, contact support. This form is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.