- English
- 日本語
About Security
Last updated 2025-03-31
The Security controls give you access to the different security products Fastly has to offer. If you have the appropriate access permissions, these controls appear when you go to Security in the navigation sidebar.
Before you begin
Be sure you know how to access the web interface controls before learning about each of the pages you'll encounter there.
About the Security pages
When you click Security in the navigation sidebar, the Security Overview page appears by default. The Overview page provides introductions to various security offerings that can help you protect your services and links you to more information about them. If you have a Signal Sciences account, you can log in to the Next-Gen WAF control panel directly from this page.
To access additional Security pages, select one of the following options:
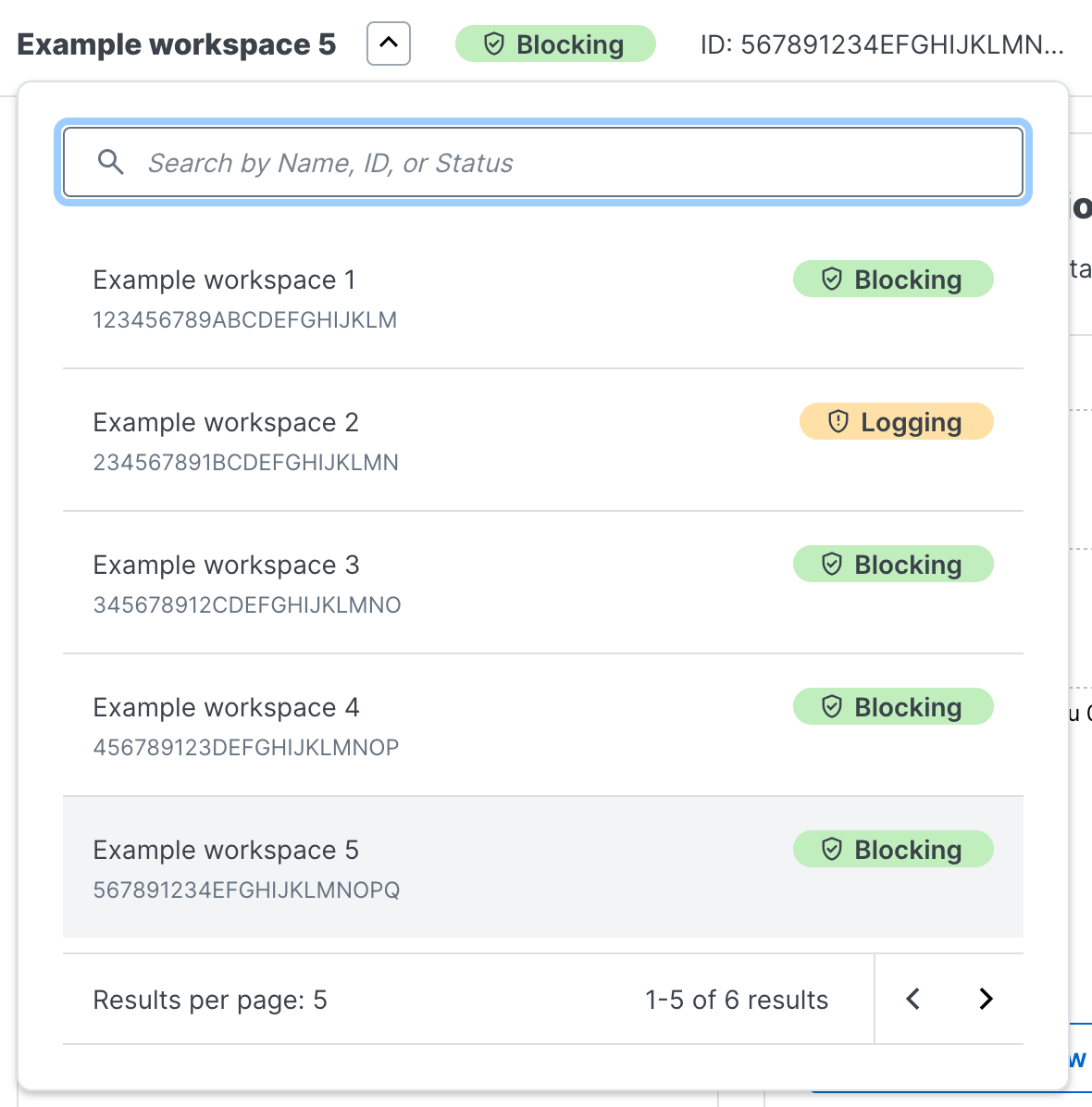
Next-Gen WAF menu, where you can monitor traffic to your web application and configure the WAF as needed. The workspaces bar persists across the Next-Gen WAF pages. From this bar, you can change your workspace and view the protection mode and ID of a workspace.
DDoS Protection menu, where you can view dashboard metrics and identified events related to DDoS attack traffic when you've enabled DDoS Protection on at least one service.
DDoS mitigation page, where you can learn more about our DDoS mitigation options. Fastly’s high-bandwidth globally distributed network was built with “always-on” DDoS mitigation designed to absorb DDoS attacks. You can also purchase a DDoS Protection and Mitigation Service that provides additional Fastly resources to assist you with mitigating the service and financial impacts of DDoS and related attacks.
TLS management menu, where you can find controls for adding HTTPS to your domains, adding additional privacy and data security to your services. You can either upload your own TLS certificates or have Fastly manage this for you.
Edge rate limiting page, where you can implement a rate limiting policy to control the rate of requests sent to your origin servers.
Bot management page, where you can review potential abusive bot activity on your network.
Client-Side Protection menu, where you can inventory and control the resources (e.g., scripts, images, and fonts) that load on an end user’s browser from defined areas of your web applications.
Security products note
No security product, such as a WAF or DDoS mitigation product, including those security services offered by Fastly, will detect or prevent all possible attacks or threats. As a subscriber, you should maintain appropriate security controls on all web applications and origins. The use of Fastly's security products does not relieve you of this obligation. As a subscriber, you should test and validate the effectiveness of Fastly's security services to the extent possible prior to deploying these services in production, continuously monitor their performance, and adjust these services as appropriate to address changes in your web applications, origin services, and configurations of the other aspects of your Fastly services.What's next
Dig deeper into details about all areas of the web interface before you move on to working with services.Do not use this form to send sensitive information. If you need assistance, contact support. This form is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.